Unlike banks and major email providers who've implemented strong passwords, 2-factor authentication and anti-phishing provisions, most retailers remain wide-open to cybercriminals.
Allowing weak passwords exposes you to fraud but not for the reasons you think
You already know that, if users can use passwords like 'password' or 'abc' or even dictionary words, hackers can brute-force guess them over time. You might think you require strong passwords with uppercase letters, digits and punctuation marks but most users just do the simple thing – 'password' becomes 'Password1!', which is predictable and not really much stronger.
But brute-force guessing is not even the real threat.
Paradoxically, the real problem is that users CAN remember a password they
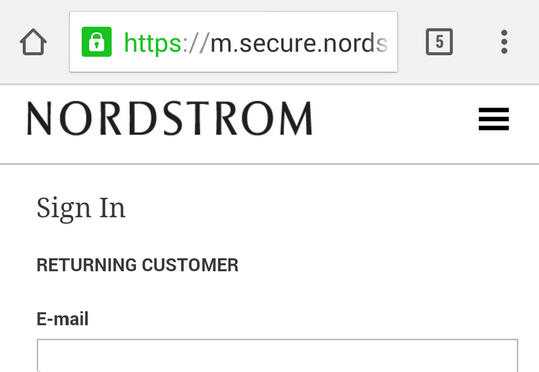
create. And this means hackers can phish the password out of them. On the small
screen of mobile devices even a savvy user will think this is the real
Nordstrom site and not actually https://m.secure.nordstrom.com.hacker.com and
will enter her password there.
Learn more about week vs strong passwords on our Blog …
Because
users tend to use the same password everywhere, storing user-created passwords also
makes your database an attractive target for hackers even if you don't store
full credit card numbers.
CardPass defends you against phishing and Cross-Site Request Forgery
CardPass uses various cryptographic techniques to protect you and your customers against hackers with unique approaches for desktops and smartphones that balance security and usability.
Vast majority of your return customers will be 2-factor-authenticated AND verified that they are not being phished completely seamlessly.
As an anti-phishing measure, a small percentage returning on a new non-smartphone device will only have to follow a link emailed to them and only if they need to change the shipping address.